In my Computer Science course we recently were required to write a program for encryption and decryption of text. The basis of this problem is an understanding of ascii codes and their function as a way of encoding text. ‘A’ = 65 and ‘Z’ = 90 with characters up and down in value. This table makes it so that a computer only has to read the value and then output the image of the character saving the user time and the computer space.
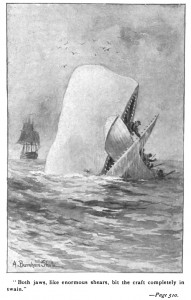
The beauty of such a system is that it can be manipulated. The first 200 bytes of Moby Dick –
MOBY DICK; OR THE WHALE By Herman Melville CHAPTER 1. Loomings. Call me Ishmael. Some years ago--never mind how long precisely--having little or no money in my purse, and nothing particular
quickly becomes something meaningless –
PUKe/V^[fYAsyJÅxxVêÑÄéäUU[[ñ–z•≈’” ⁄èø⁄‰ÒÁÌÏóóùù££flÁ„ı¸—ÂÂ⁄
0343;7FÂÂÎÎÒÒ.O]`gb LyqypwÅF;qêëåJ¶ï\†©¥uxº∂ ºÃ}ÕÑÕå◊·ÏòÁÌÔÎß˙ıˆ
“’(&" 00>A<8ıHN˛PTX]_Ypfn#sÇ,ááãÄJAÖïéMû¢™°•≠©e∏¨¿≈Ω∫œ…¡’
when encrypted by a shift cipher.
In cryptographic terms, very similar methods have been used by Julius Caesar and even the Enigma machine (although the above code is more similar to the Enigma than a caesar cipher). The prominence of computers and ease with which I can create such a code (more or less 5 lines of code) makes tin foil wearers happy, but the bigger issue is just how easily codes(like mine) can be cracked with bigger machines.
My code is meaningless to the casual observer, difficult to the novice programmer, but milliseconds of work for the NSA. A solution for this disparity in computing power and expertise is creating keys that have such a ridiculously large amount of combinations (339,000,000,000,000,000,000,000,000,000,000,000) that it would take too long for a computer to try all the combinations (which is what they would like to be able to do).